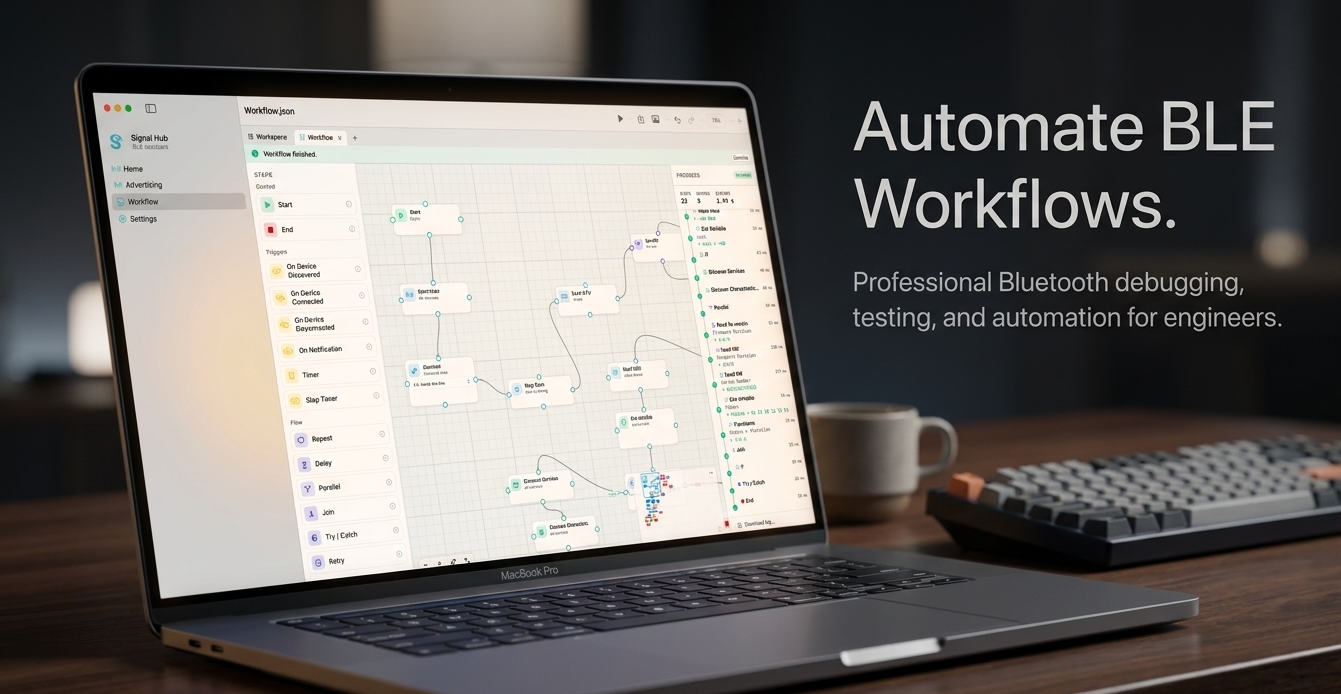
Signal Hub for Mac — the BLE workbench, reimagined
After years of shipping Bluetooth Low Energy applications, I kept hitting the same wall: the tools we use to talk to BLE devices — scan, connect, poke at characteristics, reproduce edge cases — are still stuck in the terminal-era. So I built Signal Hub, a Mac app for engineers who live in the BLE stack.
Signal Hub lets you manage concurrent BLE connections, design visual workflows that run on real hardware, simulate devices when the prototype hasn’t shipped yet, organize everything in workspaces, and export beautiful PNG / video documentation — all from one calm, elegant app.